N2 Elite
N2 Elite is sold as a game cheating product, called previously Amiiqo, an name probably too close to the original targeted game Amiibo.
I'm not interested at all in its gaming aspects but it's primarily a (multiple) NTAG215 emulator and in that respect, I'm very curious about that product :)
Intro
It's a small round passive device with one button. It can emulate up to 200 NTAG215 and can be programmed via an Android app or, if you buy their additional reader, via a PC application: N2 Manager for Windows or Mac.
Credits: I heard about it by reading a 3-page article of Patrick Gueulle in the French revue Le Virus Informatique #28. In that article, the author revealed how the emulator could be used to emulate any 7-byte UID or even a 4-byte UID (we'll come to that later) and he's providing two programs written in Basic; apparently Patrick remained true to himself ;)
N2 & NTAG Resources
- Official
- Official site has a list of shops. Mine came from Cyprus (Playmods.co.uk) and was delivered in 4 days to Belgium.
- NTAG213/215/216 datasheet
Three versions of the Android app so far:
- ed5fc865e98b33e584860b39cb70ddb6 Amiiqo_1.0.apk
- 44d1ea2fd342c7faa3af81f473eada12 Amiiqo_1.1.apk
- f39a091be603058329b085f1b0382caa Amiiqo_1.2.apk
Versions 1.1 and 1.2 contain both the same fw image to update older N2 Elite tags, see below the section about firmware.
Amiibo Resources
Nothing really useful for us but for sake of completion:
- Amiibo tags
- Unofficial sw
- Alternate manager: http://www.maxconsole.com/maxcon_forums/threads/291976-Amiiqo-Manager
- Parsing library: https://github.com/Falco20019/libamiibo
Hardware
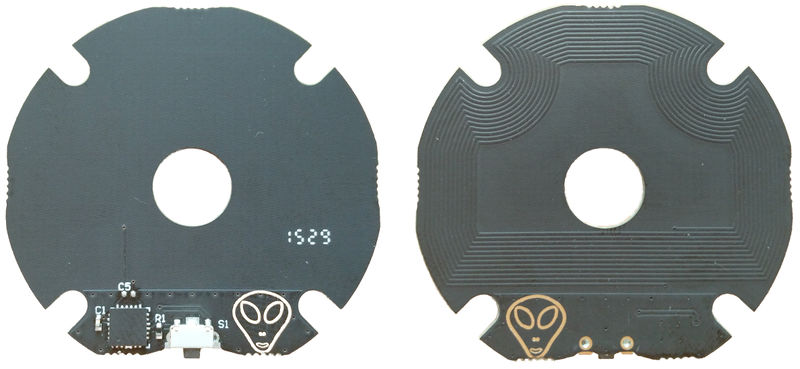
Device was sold previously under the name Amiiqo, and they insist this is the same hardware as the N2 Elite. Nevertheless there are apparently two revisions of the product:
- V1, preloaded with 10 amiibo figurines
- V2, empty, and an alien face printed on the PCB
I got a V2.
Patrick Gueulle mentions the QFN24 chip has a mark "SX3" but mine is completely black. Under the microscope he found two references on the die: "G4830H001I" and "DI 503 03".
Traces
Let's trace some transactions between the Android app and the device with a Proxmark3.
I've discarded the anticol and HALT/WUPA activities.
Discovery
Rdr | 30 02 10 8b | ok | READBLOCK(2)
Tag | ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff | |
| 37 cb | ok |
Rdr | 60 f8 32 | ok | EV1 VERSION
Tag | 00 04 04 02 01 00 11 03 01 9e | ok |
Rdr | 55 d6 54 | ok | ?
Tag | 00 01 00 03 47 3e | ok |
Rdr | 43 61 21 | ok | MAGIC WUPC2
Tag | 21 4b 87 02 52 3d 0d 10 16 3a 24 ff ff ff ff ff | |
| e4 e7 | ok |
Rdr | 3b 15 16 00 8e a7 | ok | ?
Tag | ff ff ff ff ff ff ff ff 5f d2 | ok |
When asking the app to show the tag ID it returns 214b8702523d0d10163a24.
Lock
Rdr | 46 cc 76 | ok | ? Tag | 0a a4 fe | |
Unlock
You need to press the button once the app discovers the tag and maintain it pressed. You've 2 seconds.
Rdr | 44 de 55 | ok | ? 2 secs pause. Rdr | 45 57 44 | ok | ? Tag | 0a a4 fe | |
Update number of banks
When changing the number of available banks from 1 to 2:
Rdr | a9 02 55 45 | ok | ? Tag | 0a a4 fe | |
Now the discovery phase has two such commands:
Rdr | 3b 15 16 00 8e a7 | ok | ? Tag | ff ff ff ff ff ff ff ff 5f d2 | ok |. Rdr | 3b 15 16 01 07 b6 | ok | ? Tag | ff ff ff ff ff ff ff ff 5f d2 | ok |.
Read a dump
Rdr | 30 00 02 a8 | ok | READBLOCK(0)
Tag | ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff | |.
| 37 cb | ok |.
Rdr | 30 04 26 ee | ok | READBLOCK(4)
Tag | ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff | |.
| 37 cb | ok |.
Rdr | 30 08 4a 24 | ok | READBLOCK(8)
Tag | ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff | |.
| 37 cb | ok |.
...
Rdr | 30 80 0a 2c | ok | READBLOCK(128)
Tag | ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff | |.
| 37 cb | ok |.
Rdr | 30 84 2e 6a | ok | READBLOCK(132)
Tag | ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff ff | |.
| 37 cb | ok |.
Write a dump
Rdr | 1b ff ff ff ff 63 00 | ok | PWD-AUTH KEY: 0xffffffff Tag | 80 80 64 16 | |. Rdr | a5 00 00 04 c5 a8 e1 69 44 | ok | INCR(0) Tag | 0a a4 fe | |. Rdr | a5 01 00 da aa 2b 80 d9 8d | ok | INCR(1) Tag | 0a a4 fe | |. Rdr | a5 02 00 db 48 00 00 95 62 | ok | INCR(2) Tag | 0a a4 fe | |. Rdr | a5 03 00 e1 10 12 00 e2 15 | ok | INCR(3) Tag | 0a a4 fe | |. Rdr | a5 04 00 01 03 a0 10 17 ce | ok | INCR(4) Tag | 0a a4 fe | |. Rdr | a5 05 00 44 03 00 fe 53 13 | ok | ? Tag | 0a a4 fe | |. Rdr | a5 06 00 00 00 00 00 e0 8a | ok | ? Tag | 0a a4 fe | |. ... Rdr | a5 85 00 ff ff ff ff a6 70 | ok | ? Tag | 0a a4 fe | |. Rdr | a5 86 00 ff ff ff ff db 7c | ok | ? Tag | 0a a4 fe | |.
Commands
We'll present the commands understood so far, exemplified with pn53x-tamashell scripts (to be used with libnfc and a compatible reader)
NTAG Commands
0x3C: READ_SIG
Read ECC signature of NTAG.
Syntax:
3c
#!/usr/bin/pn53x-tamashell // Please put N2 Elite on reader NOW 4a 01 00; Select tag 42 3c; Read ECC signature
N2 special commands
0x3B: N2_DUMP_FAST
Similar to 0x3A FAST_READ but with one extra parameter to specify the bank number so this command can access directly the 200 banks.
Syntax:
3b <start page> <stop page (included)> <bank>
Banks don't need to be active to be accessed.
Theoretically a bank could be accessed in one single command but it depends on the reader. With libnfc readers, don't read more than 63 pages (252 bytes) at once.
#!/usr/bin/pn53x-tamashell // Please put N2 Elite or NTAG on reader NOW 4a 01 00; Select tag 42 3b 00 1f 00; start of bank #0 42 3b 20 3f 00 42 3b 40 5f 00 42 3b 60 7f 00 42 3b 80 86 00 42 3b 87 8f 00; pages above the 540 bytes of bank #0 NTAG215 42 3b 90 af 00; this is actually start of next bank 42 3b 00 1f 01; start of bank #1 42 3b 20 3f 01 42 3b 40 5f 01 42 3b 60 7f 01 42 3b 80 86 01 42 3b 87 8f 01; pages above the 540 bytes of bank #0 NTAG215 42 3b 00 1f 02; start of bank #2 42 3b 20 3f 02 42 3b 40 5f 02 42 3b 60 7f 02 42 3b 80 86 02 42 3b 87 8f 02; pages above the 540 bytes of bank #0 NTAG215 ;etc for remaining 197 banks
This is interesting! Original Android app doesn't care about ECC signature which is left = FFFF..FF but the N2 allows the ECC of a bank to be written via the 8 pages 0x87-0x8e. See command READ_SIG above.
I found no use of page 0x8f so far.
=
N2 tricks
ECC
In the N2_FAST_DUMP we saw that it contains additional pages above the 540-byte pages.
Actually some of them are used to store what is returned by the READ_SIG command:
42 3b 87 8e 00; 32-byte ECC signature of bank #0 NTAG215 42 3b 8f 8f 00; 4 unused bytes? 42 3b 87 8e 01; 32-byte ECC signature of bank #0 NTAG215 42 3b 8f 8f 01; 4 unused bytes?
Example:
#!/usr/bin/pn53x-tamashell // Please put N2 Elite on reader NOW 4a 01 00; Select tag 42 a5 87 00 00 01 02 03; Write over bank #0 ECC 42 a5 88 00 04 05 06 07 42 a5 89 00 08 09 0a 0b 42 a5 8a 00 0c 0d 0e 0f 42 a5 8b 00 10 11 12 13 42 a5 8c 00 14 15 16 17 42 a5 8d 00 18 19 1a 1b 42 a5 8e 00 1c 1d 1e 1f 42 3c; Read ECC signature
ShowID
When Android app discovers a N2 tag, it issues what I call a N2_INFO to see how many banks are active, then it issues commands such as:
42 3b 15 16 00; Read 8 bytes from address 0x15 to address 0x16 bank #0
to discover the ID of the Amiibo figures that are stored, because actually the ID is stored in 8 bytes from page 0x15, so we can also get it from the currently active bank, or from an original figure, with:
42 30 15; Read 16 bytes from address 0x15