Hack.lu Writeups
2012 CTF by Fluxfingers
It was again a great moment of fun to participate to this year's CTF organised by Fluxfingers @ Hack.lu 2012
2012 T-Shirt contest
This one is quite apart from the other challenges for several reasons:
- The challenge was actually printed on participants' t-shirts, as of last year
- Surprisingly enough, only
23 teams over the 290 who scored at least one challenge managed to solve it!! (none of the top 10, they were teams #50,#62#57 and #83) - The challenge was the only one not designed by Fluxfingers team but... by myself, with the help of Alex to design the actual T-Shirt
Still I played the ctf fairly, proof is that even my team (woyouyizhixiaomaol=我有一只小毛驴) didn't find the solution ;-)
I must admit, the challenge was easier for local people than for remote people, reason is that a list of words was written on the T-Shirt while online a patchwork of unrelated images was visible.
On first evening, as no one solved it yet, we added an extra hint in the challenge description.
On last morning, as no remote team managed to solve it, we also published a picture of the T-Shirt for remote teams. Apparently it didn't help...
Here is it:
28 - T-shirt
Same as local T-shirt challenge: https://ctf.fluxfingers.net/challenges/noclue.png
Send your answers to (masked email on this wiki as it's too late and we hate spammers)
Hint: "It was in use sometime ago" #ctf #infosec
Hint: https://ctf.fluxfingers.net/challenges/IMG_4924.JPG
Here is noclue.png:
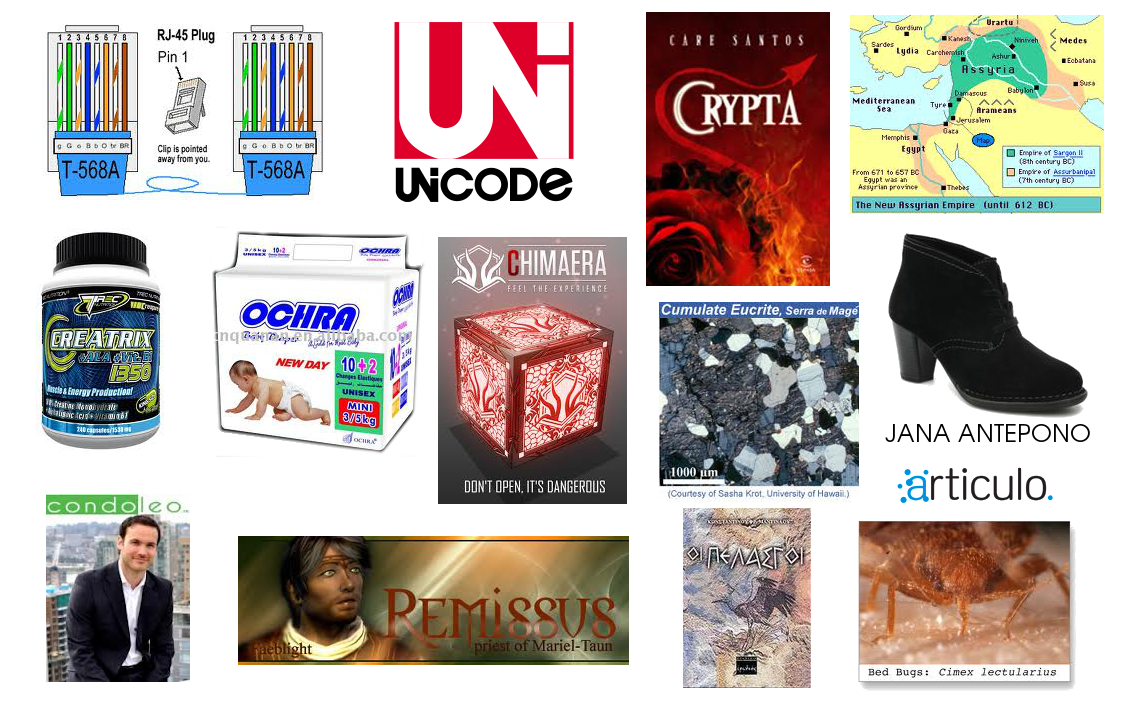
Each element represents one word.
Maybe you don't guess the exact right word for each of them, maybe not exactly in the right order, but it doesn't really matter as with a few words, it's enough to find the trick as we will see later.
So if we do the exercice we get something like:
RJ45? / unicode / crypta / assyria? / creatrix / ochra / chimaera / cumulate eucrite / jana antepono / condoleo / remissus / Πελασγοί=pelasgoi / articulo / cimex lectularius
First two seems to refer to known technologies while all the rest seems mostly latin words
Second image is the T-Shirt itself and there you get the exact word list:
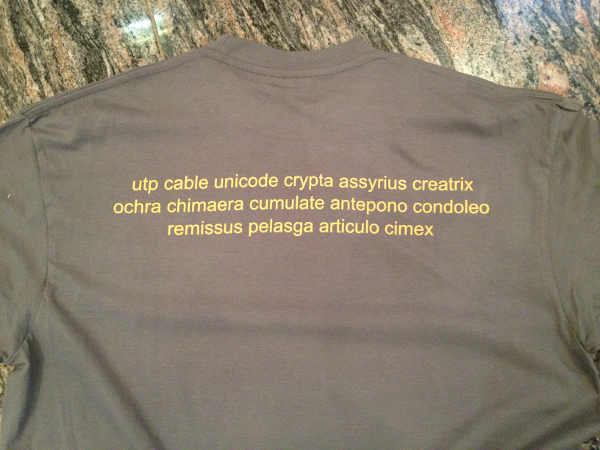
So actual word list is:
utp cable unicode crypta assyrius creatrix ochra chimaera cumulate antepono condoleo remissus pelasga articulo cimex
I heard many teams trying really many things in all possible directions, sometimes wrong ones but sometimes right:
- crypta => cryptography?? and people tried many different things but it's wrong: what you have is not a ciphertext as it's somehow "meaningful", not garbage as ciphertexts usually are, and moreover the first hint says "It was in use sometime ago". Which really means people used this kind of message in the past, it was not some pseudo-crypto I took of my hat.
- many saw that first three words are somehow separated from the rest, kind of header in front of a latin message
- someone interpreted it as those words are probably there to explain how to decode the latin message. And this is perfectly correct!
- but we are geeks and when we see utp cable unicode, our brain is too happy to know what they mean today while it seems hard to interpret! That's because thinking of the UTP you know and the Unicode you know is plain wrong :-) Remember the hint said it was in use sometime ago... not today and long ago they didn't know about Ethernet or UTF-8
- still in the funny interpretations, if you type the latin part in Google translate you get:
Assyrian vault creative ochra chimera cumulatively prefer empathize newly released article bug
and they went googling for newly released vulnerability disclosures :-) - several teams asked me if it could be related to telegraph and Morse code: could be...
So to resume the best ideas heard so far and the hint, it's about a real system used in the past to transmit messages, maybe to do with telegraph and Morse code...
I don't know for you but when I don't know stuffs I usually ask Google...
Now it all depends which words you google for but soon or later you will see an interesting hit:
Googling for crypta assyrius creatrix: first result title is Full text of ""Unicode".: The Universal Telegraphic Phrase-book
Hey! we get something about UNICODE??? Universal Telegraphic Phrase-book??? (UTP)
Even for people having thought of telegraph it works with a completely different query, not on the message itself:
Googling for unicode telegraph: third result title is Full text of ""Unicode".: The Universal Telegraphic Phrase-book
With this link you can see it's actually using a very old phrasebook.
See? Not the Unicode your brain is wired to, Not the UTP cable it's wired to, but some telegraphic cable :-)
That page is not that easy to use as such because it's kind of pdftotext output and you miss the layout.
Click on "See other format" or google again for the book title and you can find at least two versions in pdf, much more confortable to use.
E.g. check this one online
It's presented as a code of cypher words for commercial, domestic and familial phrases in ordinary use in inland and foreign telegrams
This edition was published in 1889!
Actually it's worth reading the introduction if you're curious
Why such phrasebook? Because you had to pay per word so sending "why have you not acknowledged receipt of letter?" costed 8 times more than sending "acapnon"
Even unicode is itself in the phrasebook list, intended to be used as header of the message, with some geeky self-referencing style: to decipher this message refer to the UNICODE
And so for the message we had we get:
unicode to decipher this message refer to the UNICODE
crypta have been expecting to hear from you
assyrius following is strictly confidential
creatrix exception cannot be made
ochra parcel is waiting remittance
chimaera delivery can be made at once
cumulate will bear the expense
antepono bring home with you...
condoleo dispose of it as you please
remissus can you obtain good security
pelasga be as quick as possible
articulo come as soon as you can
cimex describe exactly what you want
Teams had to submit the decoded message you see in the right column (or slight variations of it if you started from the picture and didn't get the exact words or exact order) to the given email addresses to get the points.
Congrats to ChaosMonkeys, Lesboverflow and C3L, the teams who solved this challenge!
If you tried and failed, I hope you still had fun and didn't end up totally frustrated ;-)
Any comments? Contact me
2012 zlotpy
10 - zlotpy
Gambling time. Play against the Internet Zlot Machine at ctf.fluxfingers.net tcp/2053
This challenge has two stages.
1) Medium: Investigate the contents of a saved game.
2) Hard: Get 8 (EIGHT) bonus points.
Good luck!
Hint: We have some sourcecode for you! https://ctf.fluxfingers.net/challenges/zlot.py
credits: 500 +3 (1st), +2 (2nd), +1 (3rd)
Let's investigate it:
$ nc ctf.fluxfingers.net 2053
Welcome to the Internet ZlotMachine. Enter 'T' for the Tutorial.
Your current balance is 5 credits and 1 bonus
T
The Internet ZlotMachine works like a traditional slot machine.
To get you hooked, we will give you 5 (FIVE) credits every time you visit us.
Once you have connected, there are several options:
[...]
6) Save game (Command: S)
This allows you to save the current game. You will get a string back
that you are supposed to write down somewhere. Using this string later
will allow you to resume your game, when you come back.
We use our SAFEJSON *hint hint*
7) Load game (Command: L<SAVESTRING>)
Allows you to reload a previously saved game.
[...]
S
Your games has been saved! Please write down the following save game code.
3SA7TH/9a6E4vgtY0MAuuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
This game may later be loaded with L<SAVEGAMECODE>
L 3SA7TH/9a6E4vgtY0MAuuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
Restored state.
Your current balance is 5 credits and 1 bonus
Games are saved in a base64 string with some SAFEJSON.
Inspection of the source code reveals immediately that it's actually a JSON string containing at least "bonus" and "credits" values, encrypted with AES-CBC and encoded in base64.
Probably something like {"credits": 5, "bonus":1}
Here is the decoded ciphertext:
dd203b4c7ffd6ba138be0b58d0c02eb8 c0c229df27bcab88e7f14cc472f4cecc 66cdaf066ae760d0d99ef4af7b891722 0bb2ed15bac2e5ee68f223ffd4b04fe6 fc10705ee797d3b3ac0b685b2db77bf0
So 5 blocks of 128 bits.
Here it's important to understand the CBC mode, you can check it on Wikipedia and especially the decoding: the first block is actually the random IV, to be XORed with the decryption of the next block, actually the first block of ciphertext.
So by flipping bits in the IV, we can flip the corresponding bits in the first block of plaintext.
This trick can only be made on the first block.
Let's hope the value of "bonus" is indeed in that first block.
Bonus in the saved game is 1 and we need 8.
'1'->'8' == 0x31 -> 0x38 == 0b00110001 -> 0b00111000 => we need to XOR that bonus byte with 0b00001001 == 0x9
But we don't know in which byte is located that value.
The earliest position it could get is with a JSON string starting with {"bonus":1 so the 10th byte.
The furthest we can try is on byte 16, after that we're not in the IV anymore.
Let's script it:
#!/usr/bin/env python
from base64 import b64decode, b64encode
m=b64decode("3SA7TH/9a6E4vgtY0MAuuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=")
for i in range(10,17):
print "L", b64encode(m[:i] + chr(ord(m[i])^0x9) + m[i+1:])
$ ./break-zlot.py
L 3SA7TH/9a6E4vgJY0MAuuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
L 3SA7TH/9a6E4vgtR0MAuuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
L 3SA7TH/9a6E4vgtY2cAuuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
L 3SA7TH/9a6E4vgtY0MkuuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
L 3SA7TH/9a6E4vgtY0MAnuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
L 3SA7TH/9a6E4vgtY0MAuscDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
L 3SA7TH/9a6E4vgtY0MAuuMnCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
Let's try them:
$ nc ctf.fluxfingers.net 2053
Welcome to the Internet ZlotMachine. Enter 'T' for the Tutorial.
Your current balance is 5 credits and 1 bonus
L 3SA7TH/9a6E4vgJY0MAuuMDCKd8nvKuI5/FMxHL0zsxmza8Gaudg0Nme9K97iRciC7LtFbrC5e5o8iP/1LBP5vwQcF7nl9OzrAtoWy23e/A=
Restored state.
Your current balance is 5 credits and 8 bonus
Nice one. Here's your flag: 9eef8f17d07c4f11febcac1052469ab9
Well it seems we succeeded with one single attempt :-)
Any comments? Contact me
2015
2015 Perl golf
Goal: Write a Perl program that takes a parameter as input and outputs a filtered version with alternating upper/lower case letters of the (english) alphabet. Non-letter characters have to be printed but otherwise ignored.
Example:
Input Hello World! Hallo Welt! Output HeLlO wOrLd! HaLlO wElT!
Rules:
- You have 1 second.
- You have 45 (ASCII) chars.
- Do not flood the server.
The first thing is to find how the server will use your script.
Input isn't read from stdin but is expected as the first argument, so you can try locally with
perl -e 'print @ARGV[0]' 'Hello World! Hallo Welt!' Hello World! Hallo Welt!
Then come with a strategy to convert letters as asked and squeeze it.
Here is our solution:
$_=pop;s/\pL.*?(\pL|$)/\u\L$&/g;print
But here is actually how Fluxfingers designed this challenge: they tried internally, kept the best one-liner they could come with, which was 38 chars long, and extended the limit to 45 to give some room to the participants.
And the best solution Fluxfingers had in mind:
$_=pop;s/\pL/uc$&^$"^($x^=$")/ge/print
So we were one char shorter \o/
After the CTF, we got it even shorter, now 36 chars!:
$_=uc pop;s/\pL.*?\pL/\u\L$&/g;print
Actually we can go even further if we tolerate that the script doesn't always work. One can simply reload multiple times the script till the server provides a compatible input to get the flag.